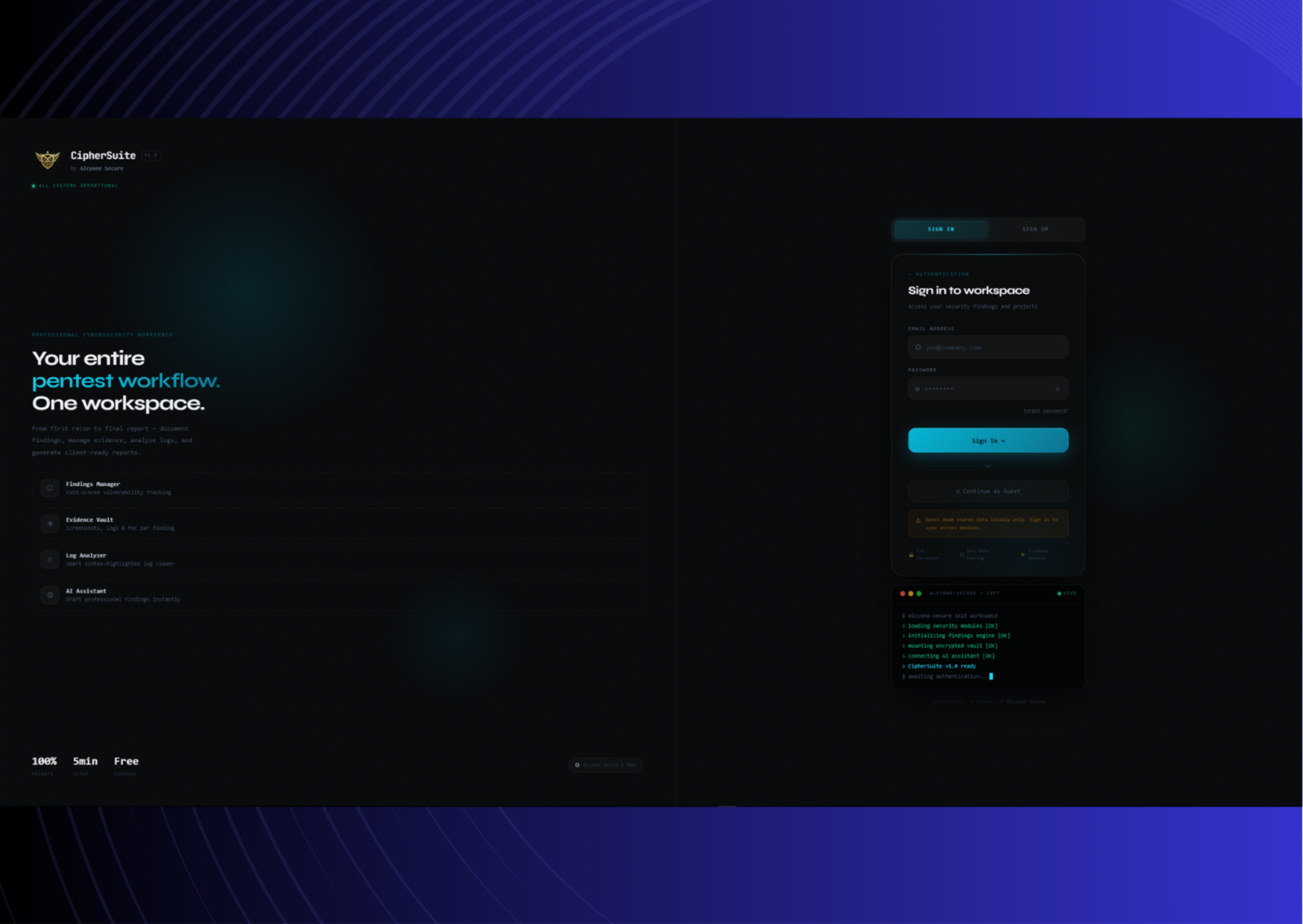
CipherSuite
Penetration Testing Management &
Security Workflow Platform
The complete cybersecurity workspace to track vulnerabilities, store evidence, and automate pentest reporting.
What is CipherSuite?
CipherSuite is a full-stack cybersecurity workspace for penetration testers, bug bounty hunters, SOC analysts, and security students. It replaces fragmented workflows—notes in Notion, evidence in Drive, and reports in Word—with one unified, dark-themed professional environment.
From first recon to final reporting, everything lives in a highly secure, isolated project space. It acts as the backbone layer for tracking findings with structured CVSS mapping, organizing evidence, and leveraging AI models to automatically assemble professional-grade client deliverables.
Technical Integrations & Ecosystem
CipherSuite operates as an integrated hub, directly connecting your scanner outputs, AI engines, and local environments.
Direct Scanner Parsers
Natively parse and ingest output directly from Nmap XML, Nessus, and Burp Suite. Our parsing engine maps raw output into structured findings instantly.
Anthropic Claude AI Integration
Under the hood, our reporting engine securely calls the Anthropic Claude API to analyze technical evidence and draft pristine executive summaries and technical narratives.
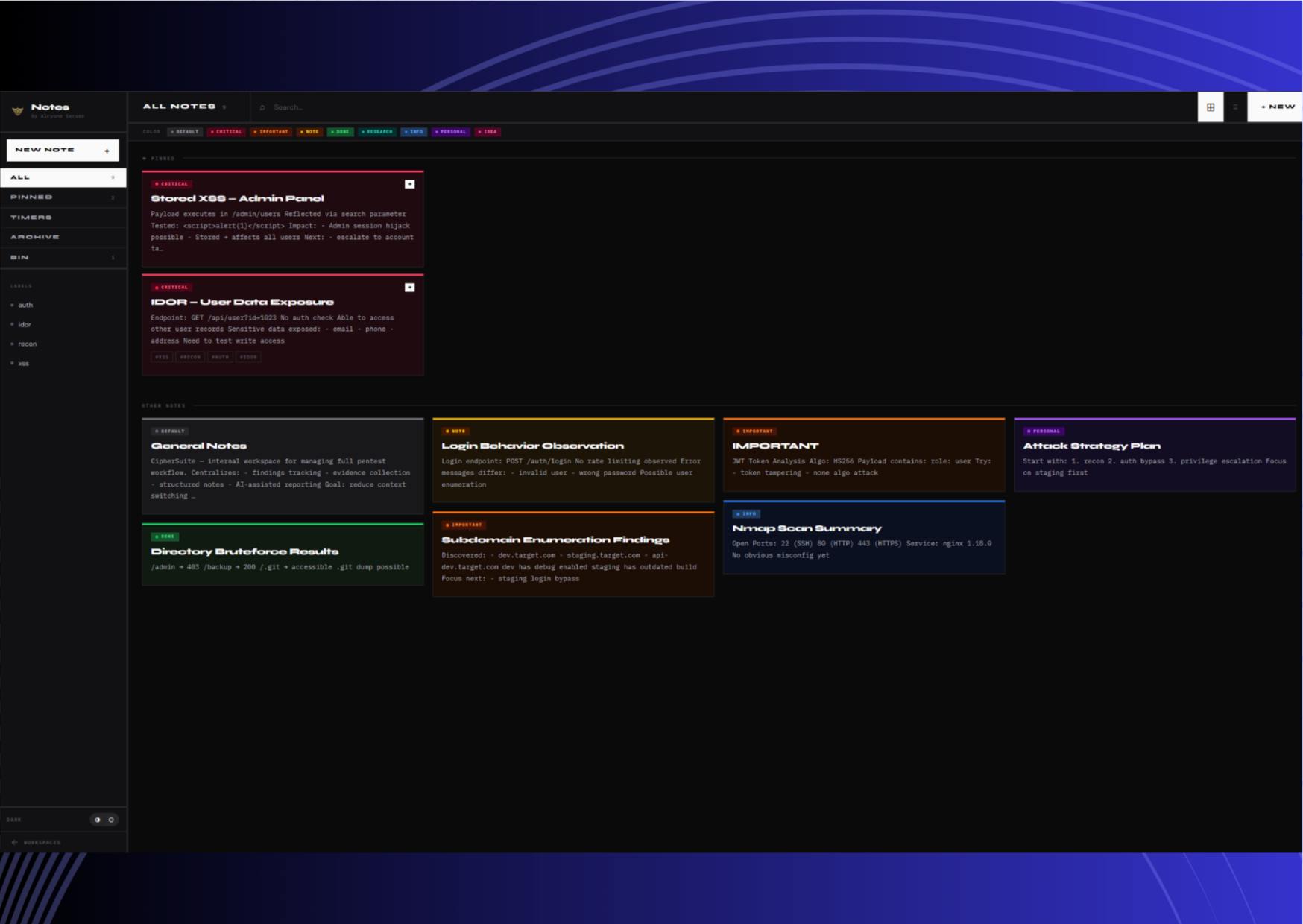
Ephemeral & Secure Notes
The markdown notes system features split previews, 1.5s debounce autosaves, specialized "local-only" flags that prevent cloud syncing, and auto-delete self-destruct timers for highly sensitive data.
Zero-Trust Project Isolation
Data is ring-fenced at the project level. Utilizing Firebase Security Rules and strict auth configurations, client engagements remain functionally isolated from one another.
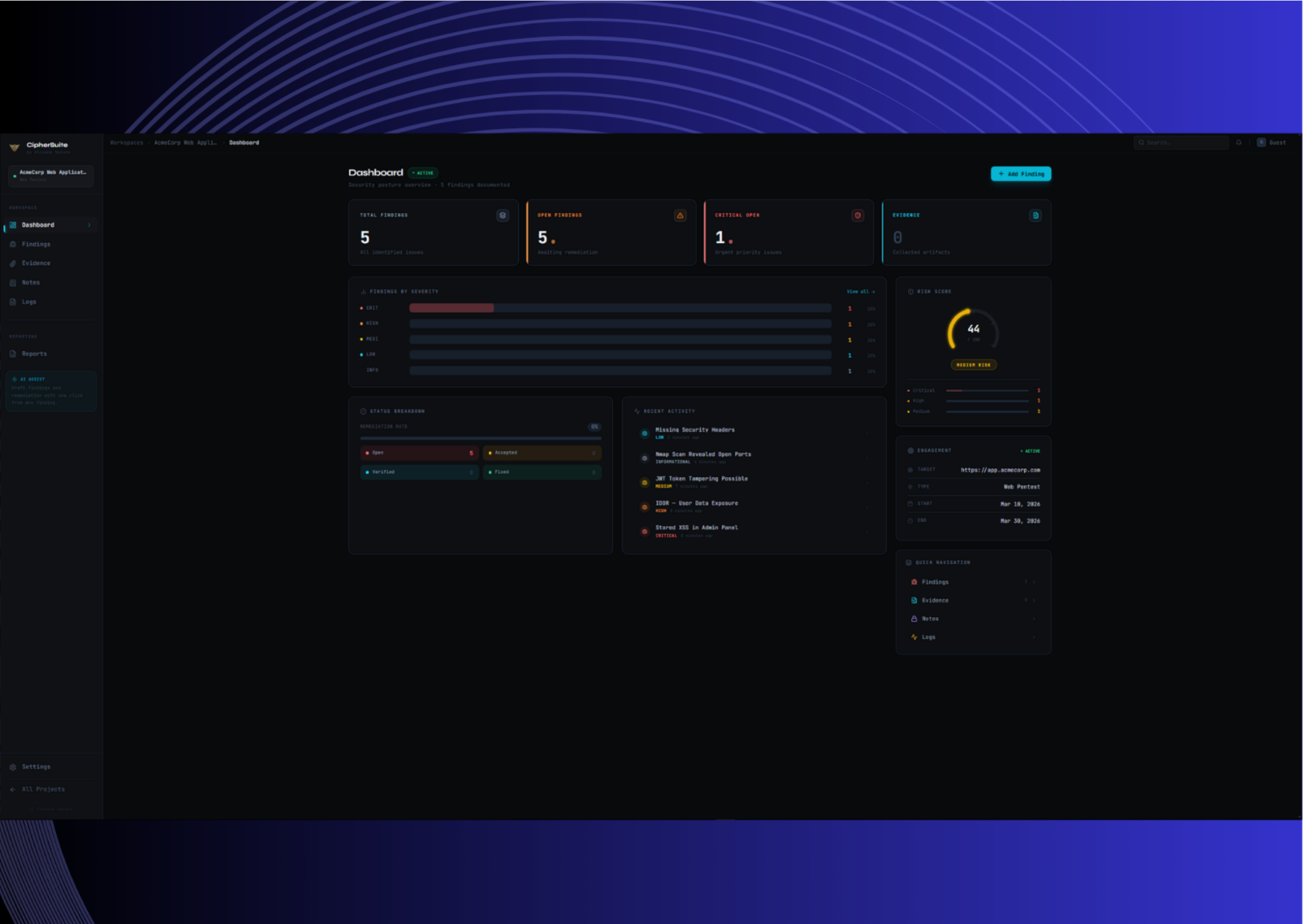
Centralized Dashboard Overview
Monitor your entire cybersecurity workspace at a glance. Users can see active projects, evaluate immediate risk status, and track penetration testing progress seamlessly in one place.
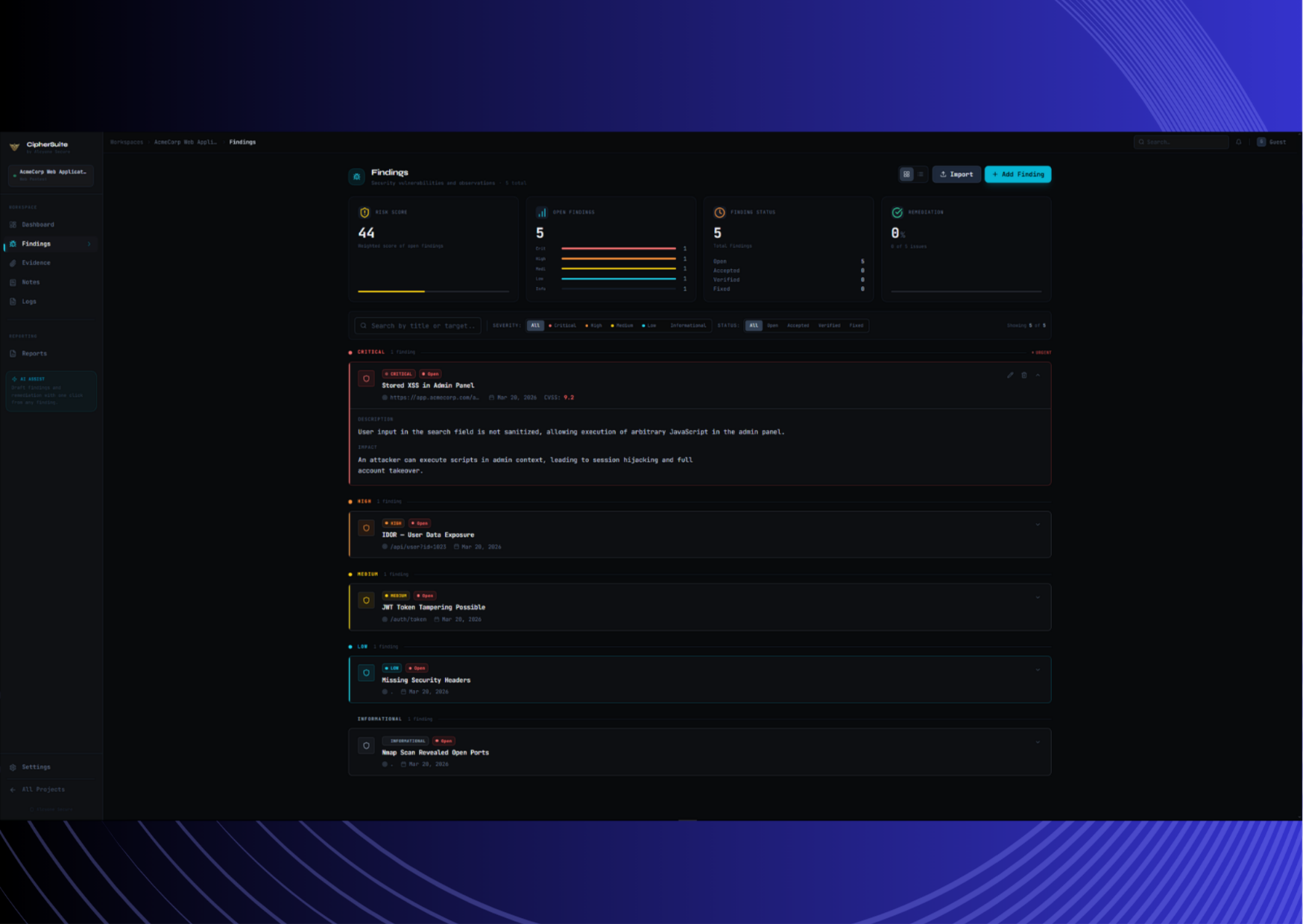
Vulnerability Tracking Tool
A dedicated findings management interface. Vulnerabilities can be tracked with CVSS severity, status, affected assets, and actionable remediation details.
Security Notes & Evidence Management
Our secure security notes tool ensures users can store proof-of-concept data, terminal logs, and highly technical notes without losing context between tools.
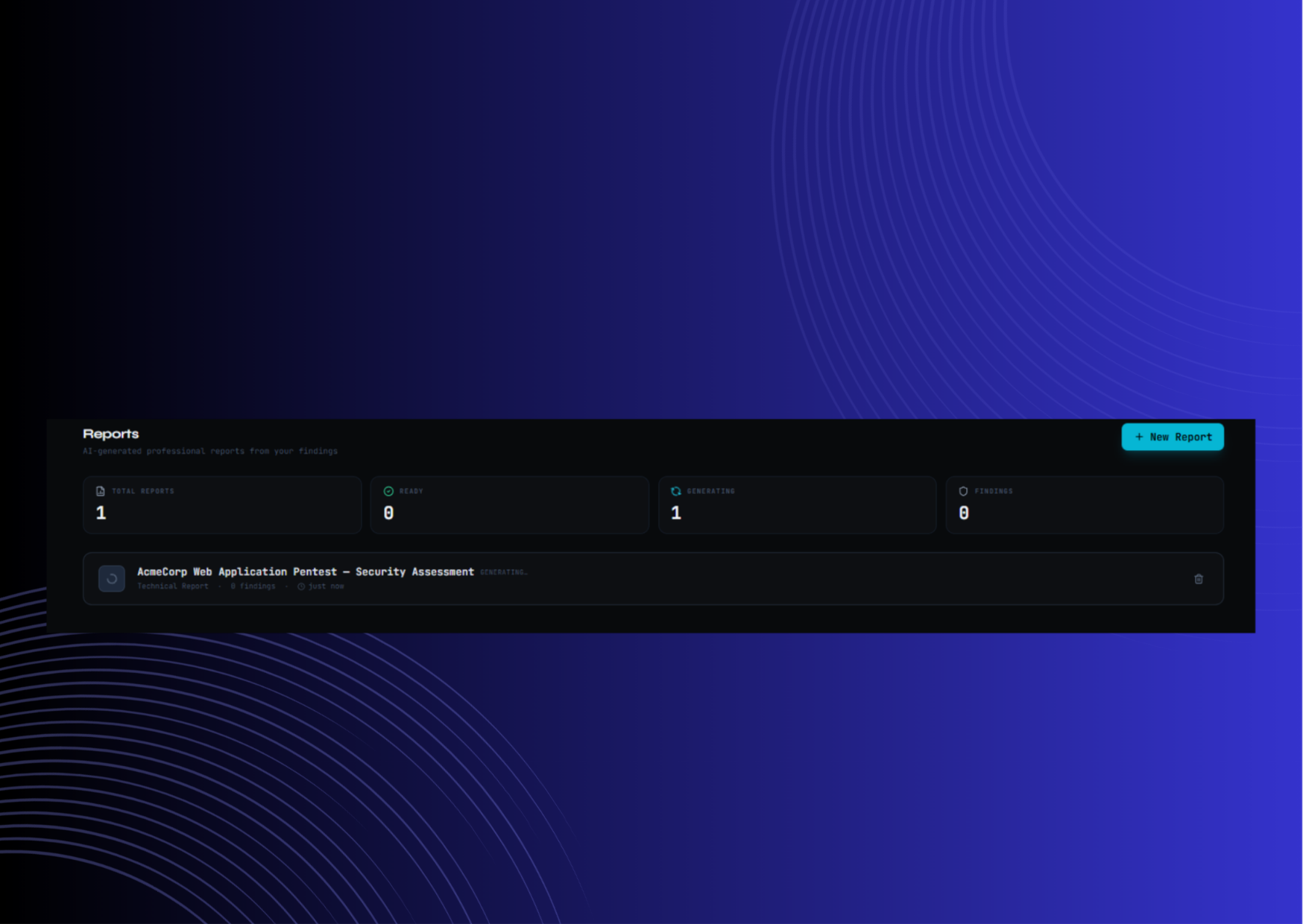
Automated Pentest Reporting Tool
Ditch the formatting struggles. Professional, client-ready security reports can be generated automatically from your existing findings data and raw evidence.
Built for Every Security Workflow
Penetration Testers
Perfect for full-time consultants managing client engagements. Consolidate your toolkit to rapidly document findings, log evidence, and export comprehensive client reports in minutes.
Bug Bounty Hunters
A specialized bug bounty management software mode. Track your program scopes, submission states across different platforms, and earnings all from one dashboard.
Security Teams
Internal IT and security teams utilise the vulnerability tracking software to continuously log internal assessment findings, track remediation, and retain a permanent audit trail.
Cybersecurity Students
Learn the discipline of structured security documentation via the CTF Mode. Manage challenges, flags, and write-ups using professional workflow scaffolding.
Enterprise Architecture & Tech Stack
CipherSuite operates as a high-performance modern web application utilizing server-side rendering and resilient cloud infrastructure.
Frontend Engine
Next.js 14, TypeScript
Fully typed React App Router with highly optimized SSR. UI components leverage Tailwind CSS and shadcn/ui to maintain the dark war-room aesthetic.
Database & Sync
Firebase Firestore
A highly scalable NoSQL document database providing real-time data synchronization, offline tracking support, and immutable audit trails.
AI Processing
Anthropic Claude API
Integrated LLM calls to distill highly technical scanner outputs, code snippets, and scattered notes into coherent, structured report narratives.
Evidence Vault
Firebase Storage & Auth
Secure cloud blob storage governed by aggressive IAM and Firestore Security Rules, ensuring binary evidence is heavily restricted based on project association.
CipherSuite vs Other Tools
Why general productivity software falls short for serious penetration testing and security reporting.
General Productivity Software
- Spreadsheets: No way to attach proof-of-concept images cleanly. Formula-based CVSS scoring is tedious and error-prone.
- Notion: Lacks strict security formatting constraints. Difficult to compile scattered markdown pages into a client-ready Word or PDF pentest report.
- Jira & Trello: Designed for software development, not security assessments. Cannot naturally parse Nmap logs or Nessus outputs.
CipherSuite Workflow
- Dedicated Data Model: Findings inherently hold CVSS logic, severity rankings, and distinct Remediation fields.
- One-Click Reporting: Findings and attached evidence are seamlessly compiled into standard pentest report templates automatically.
- Direct Import: Drag and drop Burp Suite, Nessus, and Nmap XML outputs to populate your vulnerability tracking dashboard instantly.
